Auth Systems - What are they?
If you own an email address or an account on any website/app, you have interacted with an authorization system before.
I'm talking about login screens like these:
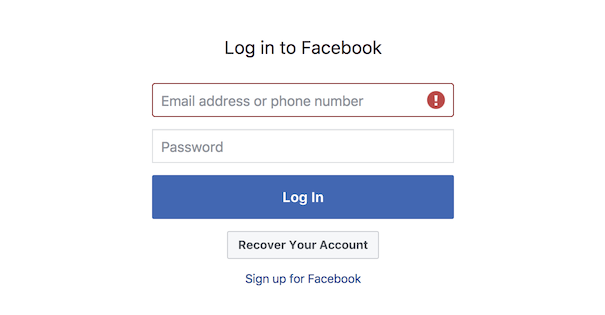
These login screens are so common that non-devs I work with tend to take them for granted, without understanding the complexity of the auth system underneath. Not their fault, but auth systems are difficult. Jeff Atwood's post on the God Login should give you a good idea, and that's just one part of an auth system.
So what is an auth system?
It's a system in place to protect a resource from unauthorized access.
A resource can be virtually anything: a web page, a Facebook Post, an Instagram Image, a Google Docs Document, etc.
Example: Let's say you've shared a private Google Docs document only with Jane. The job of an auth system, in this case, is to ensure that only Jane can access that document.
An auth system determines if a request to a resource should be authorized based on certain rules set on that resource. The rules could either be predefined or set by the owner of the resource. In our example, the rule is that no one can access the document except for Jane.
Authentication
The auth system knows that only Jane can access the document, since that's what the rule for the document [resource] says. So, when someone accesses the document, how does the auth system know if that someone is Jane or not? This is a problem because the auth system is just a piece of software, and there's no way for it to know the actual person trying to access the document. This is where authentication comes in.
Authentication is the process of identifying a person using a challenge. The most common way to authenticate (identify) someone online is through a login form.
Authentication is a means to find who is requesting a resource. The auth system can then determine if the request should be authorized depending on the rules set on the resource.
Update: Note that authentication implies consent whereas identification does not. This is why the words authentication and identification cannot be used interchangeably (like I did). Identification is done by matching the user's claims (name, date of birth, permanent address etc.), but authentication is done by presenting a challenge to the user that only he can get through. In the above example the login screen is the authentication challenge.
Authorization vs Authentication
You can't have an authorization system without authorization. Authentication is, however, not always required.
Authentication only makes sense when the authorization rules are tied to identities. A good example of an auth system that doesn't require authentication is a site that can only be accessed from certain countries. Another (good) example is rate-limiting.
Conclusion
There we have it, a really brief explanation of auth systems.
I've been trying to get this right for like weeks, and finally ended up splitting it up into separate blog posts. So yeah, I'll be posting more on this topic soon :D